NYU Abu Dhabi Researchers Lay the Groundwork for an ‘Unhackable’ Microchip
NYUAD students created an unhackable computer microchip.
September 5, 2017
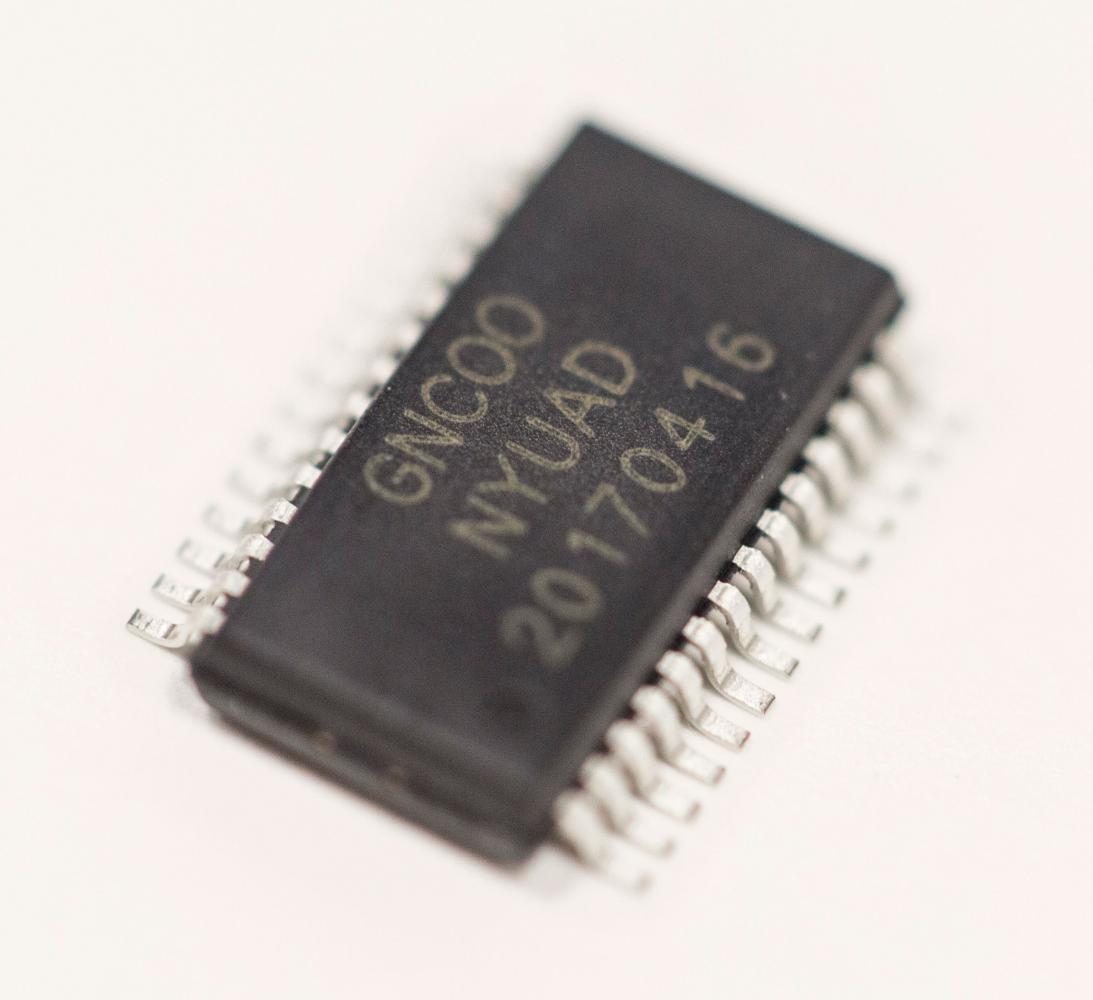
This month, researchers at NYU Abu Dhabi’s Design for Excellence Lab created what they are heralding as an unhackable microchip. The design has been in development for more than five years and aims to protect microchips from malicious attackers. The breakthrough could affect everything from personal consumer consumption to government national security.
Microprocessor security falls under a more general category called hardware security. Hardware security is the term people in security field use to distinguish physical vulnerabilities from cyber/network insecurities. While the public consciousness has opened up to the real dangers of cyber and network security, hardware security has garnered considerably less attention. Just as networks and internet connected devices are vulnerable to malicious attacks, so are the microchips used in nearly all devices.
Why chip security matters
Jeyavijayan Rajendran, an associate professor at Texas A&M and an NYU Tandon alumnus, has worked extensively on the new chip design. Rajendran said the need for secure hardware is greater than ever. While in the past microchip companies possesed full autonomy in the design, creation and production of their chips, changes in global markets have led manufacturers to outsource their microchip production, which can lead to an increased security risk.
“Until 20 years ago a single manufacturing company could design, manufacture, test and deploy that chip into the system and send to the user,” Rajendran said. “But because of advancement in technology that has led to increased costs, a single company cannot afford to have all these steps in the supply chain.”
This increase in off-site microchip manufacturing leaves a chip especially vulnerable when out of the designer’s hands. According to Ozgur Sinanoglu, an associate dean of engineering for Academic Affairs at NYU Abu Dhabi and the head of the Design for Excellence Lab, companies fear that those with malicious intent can install trojan viruses and backdoors onto the chip during off-site manufacturing. These type of attackers, according to Sinanoglu, may sell a company’s intellectual property secrets on the black market, an act called IP piracy. Attackers may also exploit vulnerabilities in hardware to slowly leak product secrets or install a kill switch, which would allow the attacker to remotely deactivate the chip.
How it works
Sinanoglu and Rajendran’s chip works by taking a standard microprocessor and locking it using a process called Striped Functionality Logic Locking. Once applied, this security measure prevents a chip manufacturer from accessing the function and mechanical details of a company chip. Many of the theoretical concepts used in the making of this prototype can be found in Sinanoglu and Rajendran’s co-written paper, “Physical Unclonable Functions and Intellectual Property Protection Techniques,” published in January.
“We first take the design we want to manufacture and then run it through our locking mechanics,” Rajendra said. “Then, [the chip] is sent to the manufacturer, the manufacturer produces the locked chip and we get the locked chip and unlock it.”
“The main idea,” Sinanoglu said, “is to show that this solution can be applied to any chip.” The prototype, which the two are preparing to show at a number of security conferences this year, took over a year to develop. The general theoretical concept and mathematical algorithms, however, have taken more than five years of work.
The future of the unhackable chip
Though Sinanoglu and Rajendran’s technology is still in what they call the “academic phase,” the need for more robust hardware security options may demand the chip [to] expand quickly. Sinanoglu admitted that at the present, cyber and network security may pose the most imminent threat to the average person but noted that hardware is not far behind, and may soon make news headlines.
For Ravendran, a more aware public does not necessarily translate to a more secure public.
“I think people are more aware of the dangers of hardware security now than they were 10 years ago, but they are not aware of any solutions,” Rajendran said.
Rajendran also said the future for the unhackable chip will require the creation of new algorithms as well as a refined design that makes it more user friendly and allows for different types of optimization for power, performance and energy. He added that these improvements take time and resources.
With security conferences and presentations fast approaching, Sinanoglu and Rajendran hope their project may catch the ears of some of the industry’s smartest and most influential minds.
If received well, consumers from all walks of life may be one step closer to a more secure technological experience.
A version of this article appears in the Tuesday, Sept. 5 print edition. Email Mack DeGeurin at [email protected]